What’s Your Interest?
Career and Educational Pathways
All Programs and Areas of Study A-Z
- Accounting
- Allied Health Education
- Anthropology
- Art
- Biology
- Biomedical Engineering Technology
- Brewing and Distillation Technology
- Business
- Business Information Technology
- Chemistry
- Communication Arts
- Computer Aided Design
- Computer Graphics Technology
- Computer Information Systems
- Cosmetology
- Criminal Justice
- Culinary and Dietary Operations Management
- Culinary Baking and Pastry Arts
- Professional Culinary Arts
- Early Childhood Education
- Economics
- Electronic Technology
- Elementary and Secondary Education
- Emergency Medical Technology
- Engineering Technology
- English
- Finance
- Fire Technology
- Geography
- Health Information Technology
- History
- Homeland Security
- Humanities
- Manufacturing
- Mathematics
- Mechatronics Technology
- Medical Assisting
- Medical Imaging
- Metallurgy & Materials Science
- Music
- Nursing
- Nutrition and Food Science
- Occupational Safety and Health
- Pharmacy
- Philosophy
- Physical Education
- Physics
- Political Science
- Psychology
- Quality Management
- Real Estate Property Management
- Sociology
- Sound Recording Technology
- Special Education
- Supply Chain Management
- Surgical Services
- Theatre
- Welding Technology
- World Languages
How Far Do You Want to Go?
- Stack Your Credentials
- Transfer Out Your Credits
- Level Up Your Skills

Stack Your Credentials
Get into the workforce quickly or work toward a degree.
Each program step builds toward a higher credential. This means you can stop at the level that’s right for you or continue upward.
Transfer Out Your Credits
Bring your credits to a four-year college or university.
Check with your Academic Advisor to see how what you’re taking here can be applied to a four-year school. In many cases, you can enter your four-year school with an impressive amount of credits.
Level Up Your Skills
Build up your skills from existing ones or try something new.
Add to your education through credit classes, non-credit classes or industry boot camps. Please see our credit and non-credit (PPL) catalogs for more information or check with your employer for opportunities with us.
View the Academic Catalog
View Personal & Professional Learning (PPL)
Become an Ocelot and Do Amazing Things
Our graduates make a positive impact in their businesses and communities. Please read their stories and watch their videos as they share how Schoolcraft College was an important part of their journey.
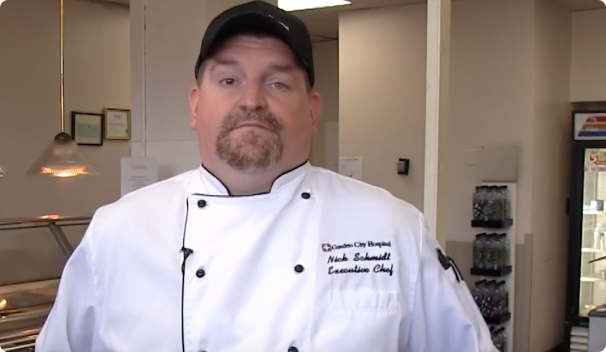
Nick Schmidt
Head Chef
Garden City Hospital
Watch Video

Marie Walker
Registered Nurse
Hegira Health, Inc.
Watch Video
Your Next Steps
Apply
Apply to become a student, then follow guided steps to register for classes.
Do
Start your journey confidently supported by professors, advisors and more.
Achieve
Use your education and experiences to make your impact in the world.